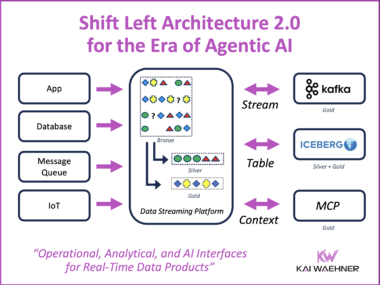
The Shift Left Architecture 2.0: Operational, Analytical and AI Interfaces for Real-Time Data Products
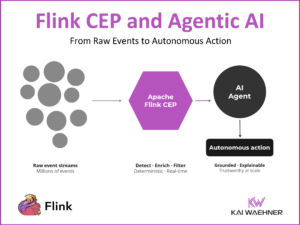
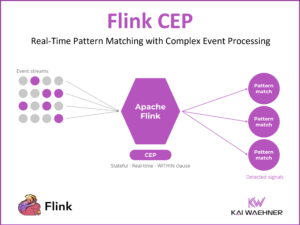
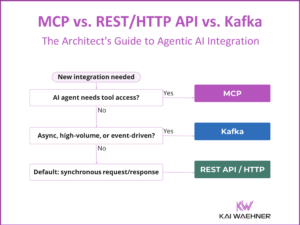
The Shift Left Architecture moves data integration logic into an event-driven architecture where governed data products are built once and served to multiple consumers. The original pattern covered two interfaces: operational via Apache Kafka and analytical via Apache Iceberg. This post introduces the third: AI applications via MCP, powered by a real-time context engine that gives AI agents access to current operational data. Governance spans the full data stack through enterprise catalog tools. Together, the three interfaces turn a single data streaming investment into the foundation for operational, analytical, and AI-powered enterprise software.